FREE Dark Data Assessment
Dark Data: Discovery, Uses & Benefits of Hidden Data
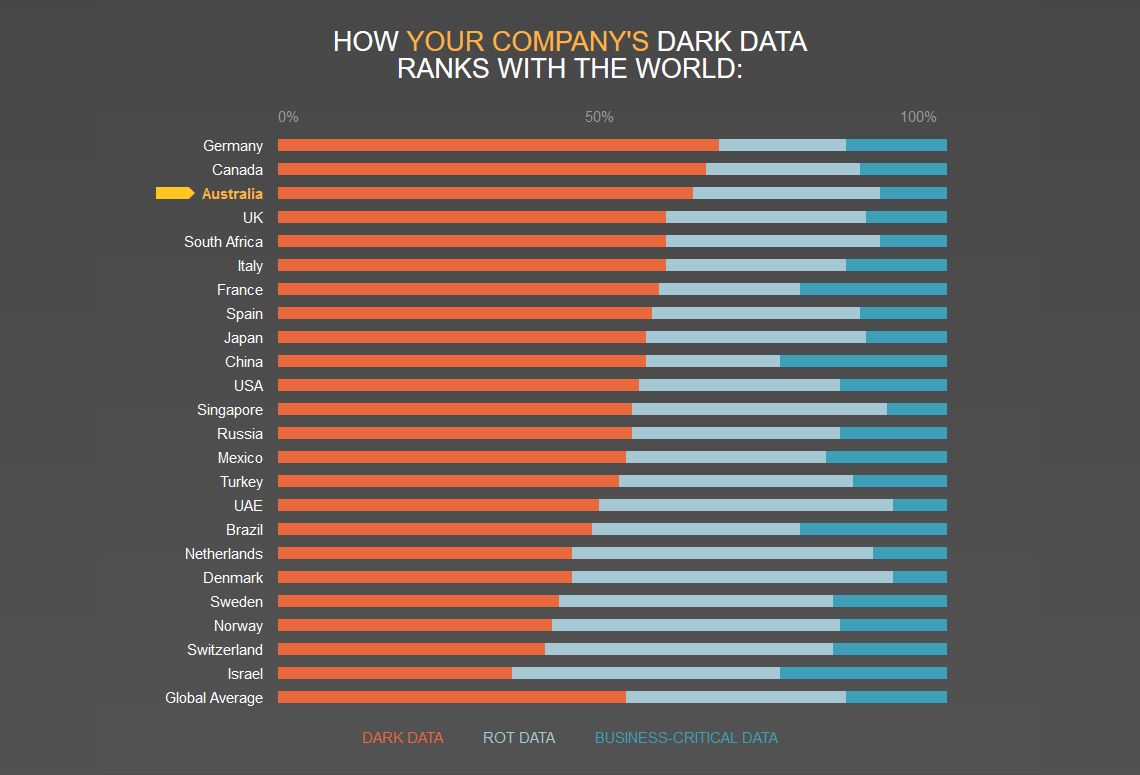
Veritas reports the worst Dark Data offenders are Germany, Canada, and Australia with respectively 66%, 64%, and 62% of their stored data defined as dark.
Next year, organisations will create 39% more data than this year. The question is: Will your budget grow 39% too?
According to Vanson Bourne, 15% of the average company’s data is considered business-critical, 33% is ROT, and 52% is unclassified—aka “dark.”
86% of IT decision makers think the amount of data they store increases the time it takes to respond to a data breach.
What is Dark Data?
Gartner defines dark data as the valuable information organisations collect, process and store in the course of their everyday operations, but generally fail to use for other purposes (for example, analytics, business relationships and direct monetising). This concept is similar to dark matter in the realm of physics, as dark data often constitutes the vast majority of an organisation's pool of information assets. Consequently, organisations often retain dark data soley for compliance-related purposes. Storing and securing data typically incurs more expense (and sometimes increased vulnerability) than value.
Why Do You Need to Uncover Dark Data?
Organisations must embark on a journey to unearth this hidden resource and distinguish between sensitive and exposed information in order to safeguard dark data from potential security threats, and facilitate access for business audits. This process of discovering and categorising dark data empowers organisations to tap into previously unused information for informed decision-making. By locating sensitive dark data, identifying authorised access, and promptly addressing any misuse, organisations can achieve the following:
Discover Dark Data
Identify and assess dark data sources through methods such as data profiling, data sampling, auditing security settings, and automated data discovery tools.
Utilise Dark Data
Leveraging dark data can help determine data ownership, improve quality assurance, detect errors, enhance privacy and security measures, and comply with regulations.
Power AI Insights
Dark data can fuel AI-powered solutions, enabling deeper and more accurate insights.
Enhance Operational Efficiency
Analysing dark data can reveal opportunities for operational improvements, such as system optimisation, predictive maintenance, and resource allocation.
Assist Compliance and Risk Management
Dark data may contain critical information for compliance and risk assessment, including risk modeling, regulatory reporting, third-party risk identification, and audit support.
Harnessing dark data offers numerous opportunities for organizations, from optimizing internal processes to improving customer support, supply chain operations, and training. To stay ahead, organizations should:
- Prepare for AI: Stay informed about AI and machine learning, identify relevant use cases, and embrace automation for efficiency and accuracy.
- Build a Data-Centric Culture: Establish the infrastructure and strategies for data-driven decision-making, infuse data analytics into strategic planning, and prioritise data visibility.
- Recruit Data Skills: Address the data skills shortage by hiring roles like data analysts, data architects, data engineers, and data scientists.
- Provide Training Opportunities: Invest in training and development for existing employees to keep up with evolving technologies and foster career growth.
How Do You Uncover Dark Data?
There are two main approaches to assessing and managing an organisation's dark data. One option involves engaging with independent experts who can thoroughly examine the data environment and conduct in-depth evaluations of unutilised and unclassified data on behalf of the organisation. Alternatively, organisations equipped with the right tools can autonomously review all their data repositories, regardless of where the data resides. This autonomous approach offers several advantages, as it allows organisations to uncover potential breaches of regulations, ascertain internal permissions (who can access what), identify gaps in data security, and uncover potentially malicious or negligent activities that could jeopardise confidential and private data. Opting for a data analytics solution can provide a more comprehensive, discerning, and precise understanding of the data, along with clearer steps for addressing any risks.
Organisations that gain visibility into its dark data will truly appreciate its business value and take appropriate measures to safeguard it. Establishing a foundational framework to "tag" or categorise this concealed data is the first step toward gaining such insights. Without this foundation, organisations struggle to adhere to data governance standards, regional regulatory compliance, provide robust security measures, or ensure data privacy for both customers and employees.
This involves organisations determining if their data is already visible and actively used—whether it falls under managed data, business-critical information, outdated redundancies, or the realm of dark data. This understanding is important as to ascertain the data's location, its nature, and the applicable standards and policies. Knowing who accesses the data and how it is (or should be) governed are integral components of the fundamental framework for classification and discovery. Following a thorough investigation, truly obsolete dark data can be scheduled for deletion, thereby reducing the required storage capacity and associated costs.
Dark data represents an untapped resource that organisations should leverage to stay competitive and prepare for a data-driven future. To do so, they must invest in data literacy, culture, talent acquisition, and employee development to maximise the value of their data assets
At Konverge, we use the leading and trusted vendor in this space Veritas to provide solutions to uncover dark data.
For a limited time only, get a FREE Dark Data Assessment on a sample of on-premise or in the cloud data.
Simply complete the form below and our Konverge consultants will reach out to you to discuss the next steps.
FREE Dark Data Assessment